Global SSO Settings
The Global SSO Settings tab provides the options to enable/disable the configurations for how your users and administrators will login using SSO. Below you will find the details for the options that are present in this tab.
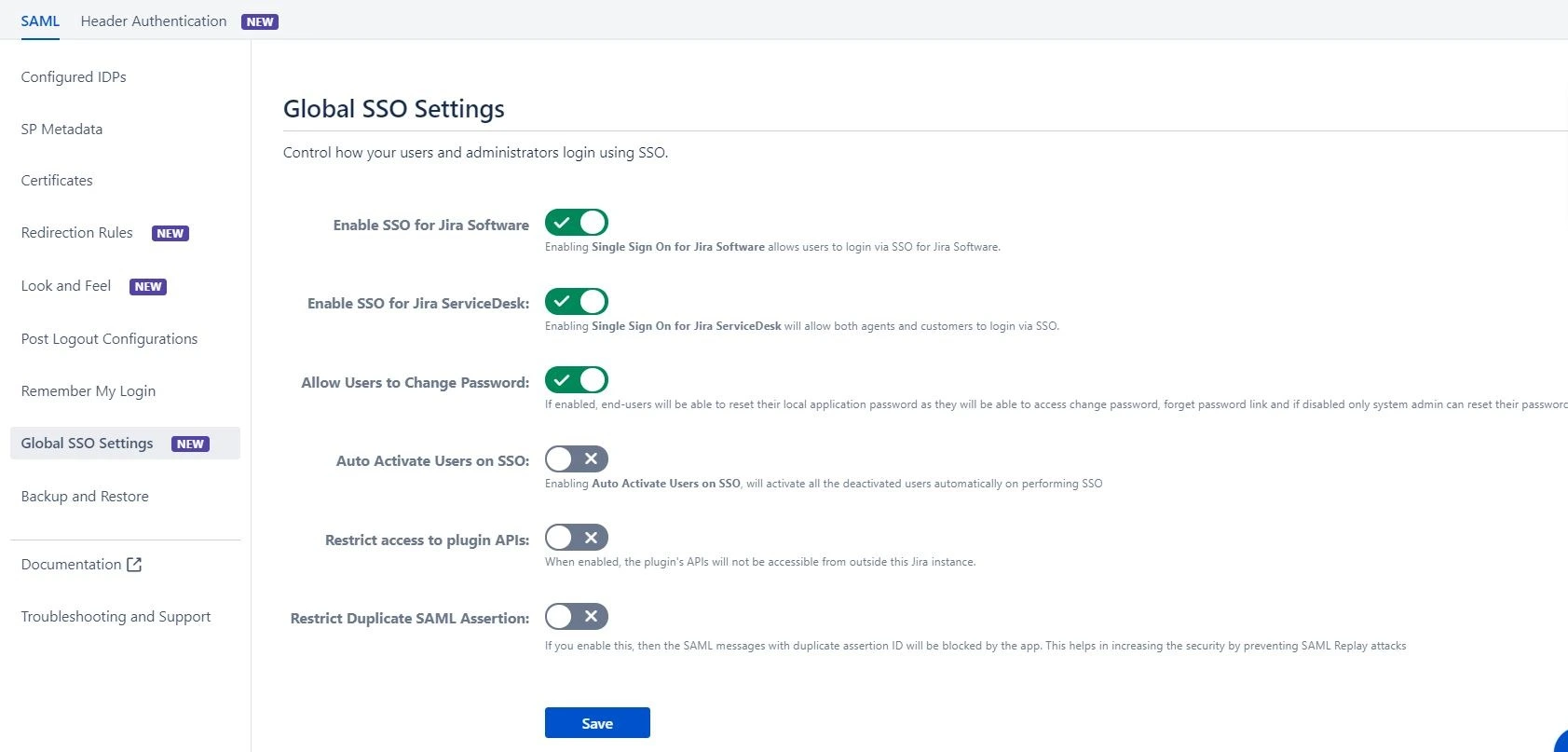
Enable SSO for Jira Software
Enabling this option will allow all your Jira software users to perform SSO. If this option is disabled, then the SSO for all the users is disabled. You can use this feature to test SSO on your environment without affecting the end users by disabling the SSO for all. Enabling/disabling this feature will override your IDP specific Enable SSO for Jira Software settings you have configured in the IDP menu.
Enable SSO for Jira Service Desk
Enabling SSO for Jira Service Desk will allow all the users from the service desk to perform SSO. Enable this only when all the users from the service desk are able to perform SSO. If your application is used only by customers, disable this feature so they can log in with their default application credentials. This feature works irrespective of the IDP specific Enable SSO for Jira Service Desk settings you have configured in the IDP menu.
Allow users to Change Password
This feature allows end-users to change their local application password. If disabled, end-users won’t be able to reset their local application password as they won’t be able to access change password, forget password link and only system admin can reset their password.
Auto Activate Users on SSO
Enabling Auto Activate Users on SSO, will activate the deactivated users who perform SSO in the application. This will ease the admin’s work as he wont have to enable the deactivated users to allow them to perform SSO.
Restrict Access to Plugin API’s
When enabled, the plugin’s APIs will not be accessible from outside of the application. This feature allows you to restrict access of the plugin’s API’s in the scope of the application instance.
Restrict Duplicate SAML Assertion
This feature allows you to restrict duplicate SAML assertion. If you enable this, then the SAML messages with duplicate assertion ID will be blocked by the app. This helps in increasing the security by preventing SAML Replay attacks.
