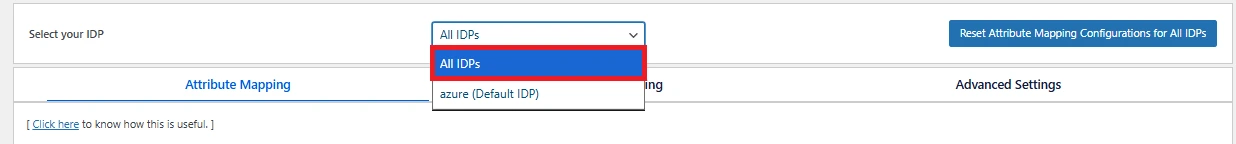
Fallback Configuration
Configuring All IDPs means setting a fallback behavior where the All IDPs configuration is applied only when no specific configuration exists for the current IDP, otherwise the IDP-specific configuration takes precedence.
Important:
-
If Attribute Mapping, Advanced Settings, or Role Mapping is configured (or even partially configured) for a specific IDP, then All IDPs configuration is completely ignored for that IDP.
-
As All IDPs do not represent any real IDP, options like test configuration, IDP Attribute list, and Role List are not provided for them.
Practical Examples: Attribute Mapping Behavior
Example 1
The following examples illustrate how the plugin selects attribute mapping when only All IDPs Mapping Configured:
Configuration:
- IDP A → no Attribute Mapping defined
- IDP B → no Attribute Mapping defined
Result:
- IDP A → uses All IDPs mapping
- IDP B → uses All IDPs mapping
Behavior:
In this scenario, All IDPs effectively acts as a global configuration, since no IDP-specific mappings exist.
Example 2
The following examples demonstrate how the plugin selects attribute mapping when a mixed (fallback) configuration is applied.
Configuration:
- IDP A → has its own Attribute Mapping
- IDP B → no Attribute Mapping defined
- All IDPs → mapping is configured
Result:
- IDP A → uses its IDP-specific mapping
- IDP B → falls back to All IDPs mapping
Behavior:
In this scenario, IDP-specific mapping takes priority when available, and All IDPs acts as a fallback global configuration when no specific mappings exist.
Example 3
The following examples demonstrate how the plugin selects attribute mapping when a partial IDP-specific mapping (edge case) configuration is applied.
Configuration:
- IDP A → has Attribute Mapping configured (but incomplete)
- All IDPs → has a complete mapping
Example Mapping:
- IDP A → maps only Username
- All IDPs → maps First Name, Last Name
Result:
- IDP A → only Username is mapped
- First Name and Last Name are not populated
Important Behavior:
- The plugin does not merge mappings
- Missing attributes from IDP-specific configuration are not filled using All IDPs
- Only the IDP-specific mapping is applied.
Practical Examples: Role Mapping Behavior
Example 1
The following examples illustrate how the plugin implements role mapping when only the “All IDPs” mapping configuration is enabled.
Configuration:
- No Role Mapping is defined for any specific IDP
- Role mapping is configured under All IDPs
Result:
- IDP A → uses All IDPs mapping
- IDP B → uses All IDPs mapping
Behavior:
In this scenario, All IDPs effectively acts as a global configuration, since no IDP-specific mappings exist.
Example 2
The following examples illustrate how the plugin implements role mapping when a mixed configuration (fallback in action) is enabled.
Configuration:
- IDP A → has its own role mapping
- IDP B → no role mapping defined
- All IDPs → mapping is configured
Result:
- IDP A → uses its IDP-specific mapping
- IDP B → falls back to All IDPs mapping
Behavior:
- IDP-specific mapping takes priority when available
- All IDPs is used only as a fallback
Example 3
The following examples illustrate how the plugin implements role mapping when partial IDP-specific mapping (edge case) is enabled.
Configuration:
- IDP A → has role mapping configured (but incomplete)
- All IDPs → has a complete mapping
Example Mapping:
- IDP A → group value is only mapped for Administrator
- All IDPs → mapped for Administrator, Editor
Result:
- IDP A → role would only be mapped according to the values configured in the IDP-specific role mapping.
- Roles will not be mapped according to values configured in All IDPs.
Behavior:
- The plugin does not merge mappings
- Missing role mapping configuration from IDP-specific configuration is not filled using All IDPs
- Only the IDP-specific mapping is applied.
Practical Examples: Advanced Settings Behavior
Example 1
The following examples illustrate how the plugin applies advanced settings constraints when only the “All IDPs” mapping configuration is enabled.
Configuration:
- No advanced settings are defined for any specific IDP
- Advanced Settings is configured under All IDPs
Result:
- IDP A → uses All IDPs advanced settings
- IDP B → uses All IDPs advanced settings
Behavior:
In this scenario, All IDPs effectively acts as a global configuration, since no IDP-specific advanced setting exists.
Example 2
The following examples illustrate how the plugin applies advanced settings constraints when a mixed configuration (fallback in action) is enabled.
Configuration:
- IDP A → has its own Advanced Settings
- IDP B → no Advanced Settings defined
- All IDPs → advanced settings are configured
Result:
- IDP A → uses its IDP-specific Advanced Settings
- IDP B → falls back to All IDPs Advanced Settings
Behavior:
- IDP-specific advanced settings takes priority when available
- All IDPs is used only as a fallback
Example 3
The following examples illustrate how the plugin applies advanced settings constraints when Partial IDP-Specific Mapping (Edge Case) is enabled.
Configuration:
- IDP A → has Advanced Settings configured (but incomplete)
- All IDPs → has a complete advanced settings
Example Mapping:
- IDP A → Attribute Restriction is configured.
- All IDPs → Domain Restriction is configured.
Result:
- IDP A → only Attribute Restriction will be applied.
Behavior:
- The plugin does not merge advanced settings.
- Missing Advanced Settings configuration from IDP-specific configuration are not filled using All IDPs
- Only the IDP-specific settings are applied.
For more information visit our WordPress SSO page.