Attribute / Role Mapping
It is the on-the-fly assignment of specific attributes / groups to your wordpress users as they are present in your IdP. When the user performs the SSO, the IDP sends over some attributes like NameID, Email, etc. which are then used to assign the users with specific functionalities like access or restrict the resources provided by the wordpress. The Attribute / Role Mapping tab allows you to enable these certain property-specific functionalities for your users during SSO.
For more details, visit the Single Sign On for WordPress page.
This tab contains the following 3 sections:
- Attribute Mapping
- Domain Restriction
- Role Mapping
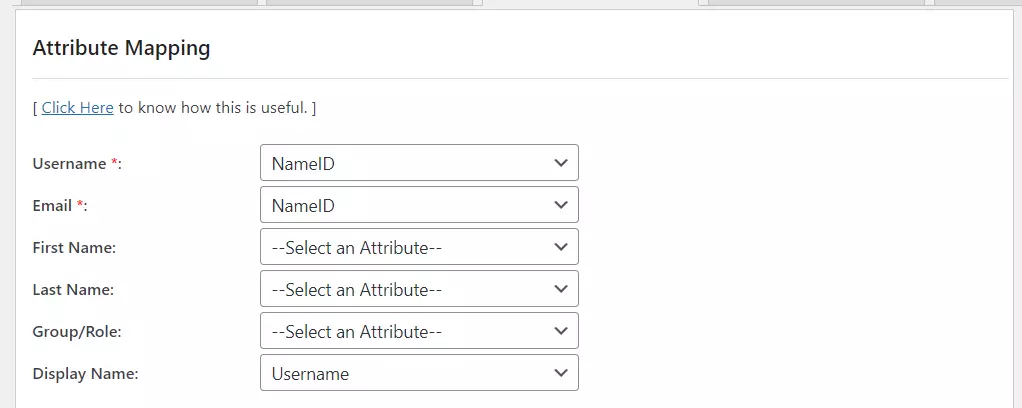
1. Attribute Mapping
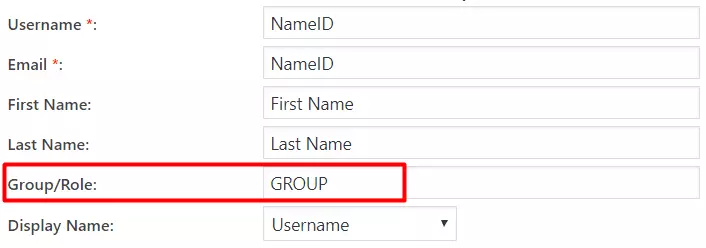
Attributes are the user details that are stored in your Identity Provider. These attributes include Username, Email, First Name, Last Name, Group/Role, Display Name, etc. The Attribute Mapping feature helps you to map these user attributes sent by the IDP to the WordPress user attributes.
- Everytime your users SSO into your WordPress site, these attributes will be automatically mapped to your WordPress user profile.
- If any existing user performs the SSO, then their wordpress account will be fetched and their profile will be updated based on attributes received from the IDP.
- By default, the Username and Email are the two basic attributes that are used for attribute mapping. Generally, the NameID value is what’s used for this purpose.
- You can choose and set attributes sent by the IDP to be mapped with WordPress attributes like FirstName, LastName, DisplayName.
- The Group/Role field can be used as a group transformation attribute. You can map the Group/Role field to the attribute name in which IDP is sending the users Security Group or Membership Information.
- Depending on the value of the Group attribute, you can assign single or multiple wordpress roles to the users. The custom roles are also supported for the mapping. Please refer to the role mapping section for more information.
Map Custom Attributes
- It provides an additional feature to Map Custom Attributes (ACF - Advanced Custom Fields) to the wordpress users. Using this feature you can map and store additional attributes received from the IDP to the wordpress user_meta table.
- You can enable the Display Attribute option for an attribute if you want to display it in the Wordpress Users menu.
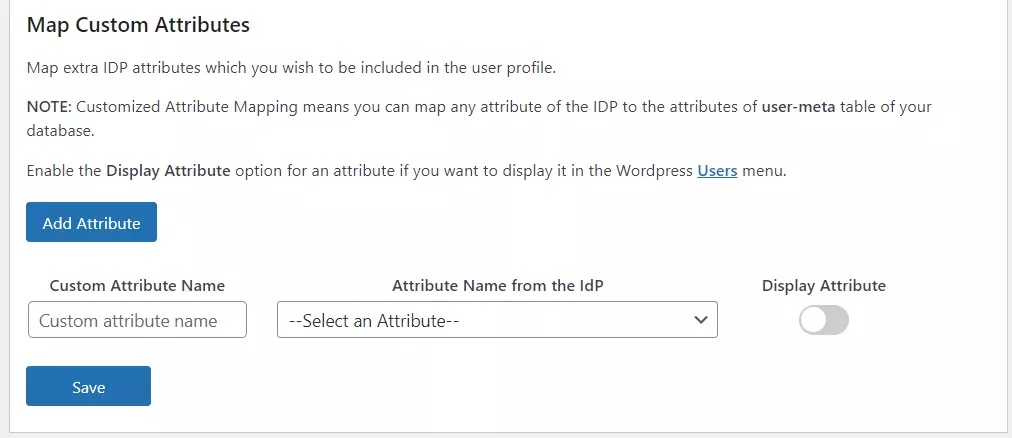
- Suppose, you want to map attributes like Phone no., City, State, Department etc., you will simply have to add these attributes in your IDP and set them up into your Custom attribute mapping to map with their equivalent attributes.
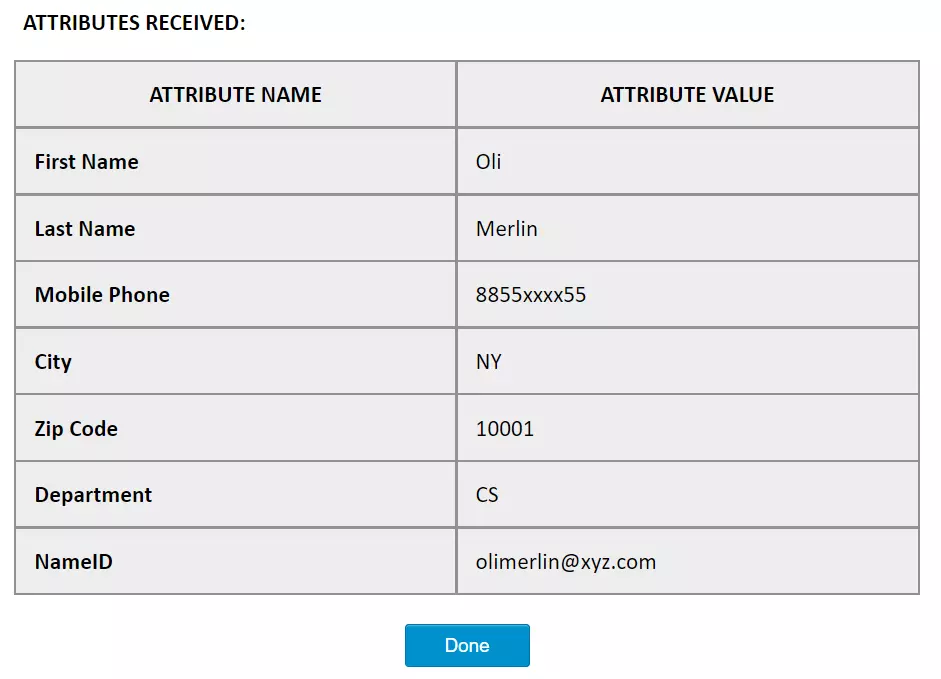
- For example, the image below shows the above attributes which are sent from the Identity Provider appropriately added and mapped to their equivalent attributes in the wordpress site.
2. Domain Restriction
- This feature can be used to restrict/allow user access to the wordpress site based on the domain of their email address.
- For the WordPress Multisite SSO Plugin, you can also restrict which group of users will have access to which subsite based on the domain of the user.
- You can provide multiple domains to restrict by entering a domain values separated by semicolon(;).
It has the following 2 ways to use this feature :
-
Allow users to login with specified domains : If enable this feature then only the users of specified domains will be allowed to login or register.
-
Deny users to login with specified domains : If enable this feature then users of specified domains will be restricted to login. Remaining all the users will be allowed to login.
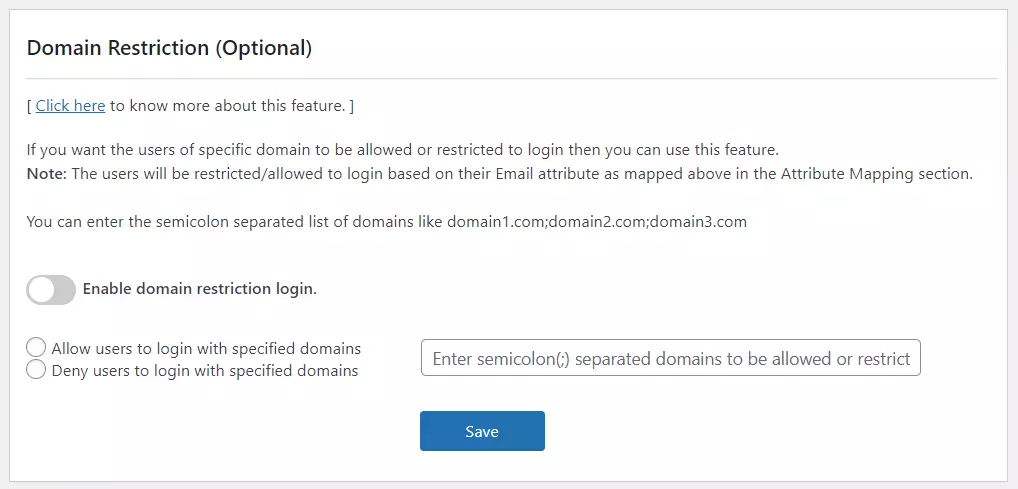
- Now, for eg. If you want users of ‘miniOrange’ (i.e. miniorange.com) to not log in to your site, then you can simply enter miniorange.com in the input tag and select radio button “Deny users to login with specified domains”.
3. Role Mapping
- This feature can be used to assign different WordPress roles to the users based on their SAML attributes. The particular roles will be applied to users once they meet the specified conditions while logging into WordPress via Single Sign-On.
- This feature allows you to provide user capabilities based on their IdP attribute Group values.
- Before enabling this setting, please make sure you’ve configured the attribute name in the Group/Role field of the Attribute Mapping section.
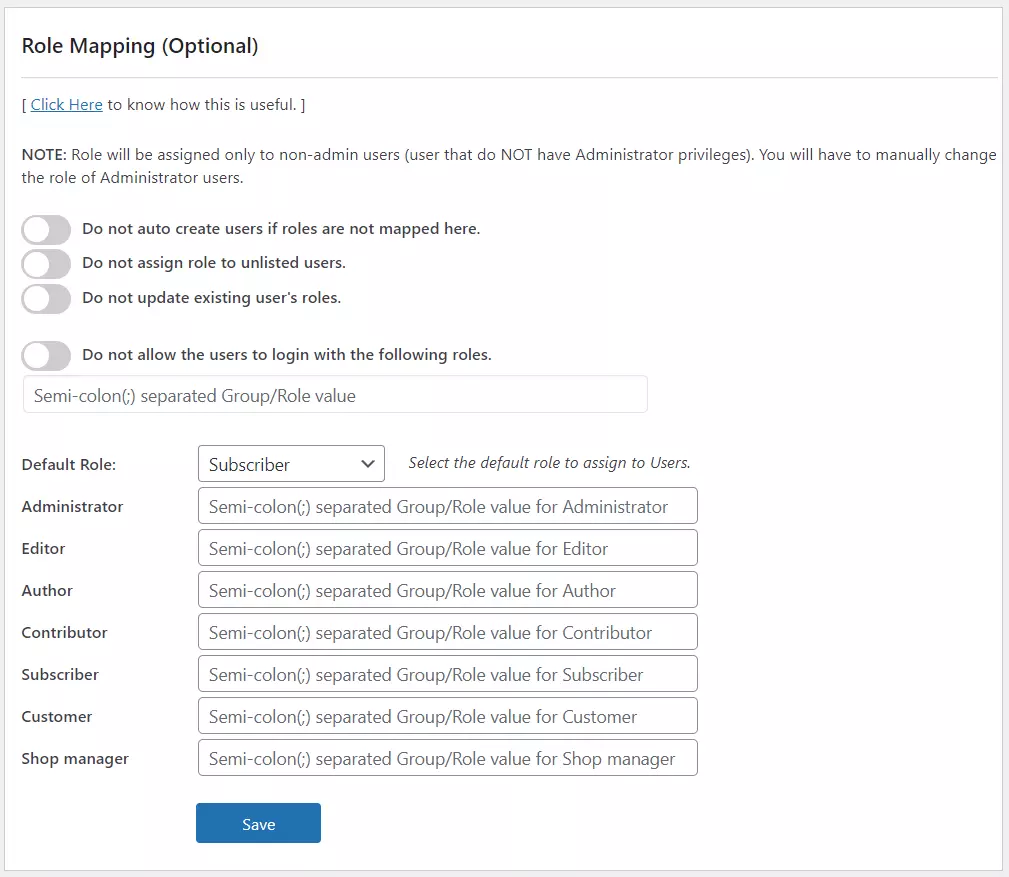
Role Mapping has the following features:
- Do not auto create users if roles are not mapped here.
- If the admin wants to create the users on the WordPress site only if their groups are mapped below, then this feature can be enabled. This won’t allow unmapped new users to access the site.
- By enabling this feature, new people not associated with any of the above groups will see the Error Message while logging in.
- Do not assign roles to unlisted users.
- This feature allows users to access the site even if their group is not assigned with any specific wordpress role. The users will have a role as None if they are not assigned.
- This feature is particularly useful incase you don’t want new users to have automatic roles assigned to them. They will be able to access the site as it would be viewed without WordPress Role.
- We also support the Anonymous login feature, in which users won’t be created at all on the WordPress site. They will be able to see the site once successfully authenticated with IDP. For more information, view the Anonymous Login addon page or contact us samlsupport@xecurify.com
- Do not update existing user’s roles.
- This feature can be enabled if the admin want existing user’s roles to persist after SSO.
- This also means their roles won’t be changed / Downgraded if they’re updated in the IDP.
- Now we have a scenario where a Teacher gets upgraded to HOD, but since the Teacher was the editor and admin does not want to change the role of Teacher from editor to author(since HOD’s are authors). This feature can be used.
- Do not allow the users to login with particular roles.
- If the admin wants users of a particular IDP group(s) to be restricted from logging in to the site, this feature can be enabled by providing the group value(s).
- This feature can be used where we have a group of students with Off-Campus Registration. They have been assigned a IDP group ‘Outside Users’ and the admin does not want those users to access the site.
- Option to select the default role to assign to users.
- This feature is used to set a default role to users who are not mapped here. It will automatically set the default role to the new users.You can choose any of the roles listed to be set as default.
This feature allows you to provide user capabilities based on their IdP attribute values.
- You can assign a default role to the users.
WordPress has 5 pre-defined roles :
- Administrator
- Editor
- Author
- Contributor
- Subscriber
Your custom roles, if added any, will also be displayed in the role mapping section.
In the attribute mapping section, we have mapped the IDP attribute having name as GROUP in the Group/Role field.
For more information visit our SSO for WordPress page.